
Managed WARP Deployments
Streamlining Cloudflare WARP Managed Deployments on Windows
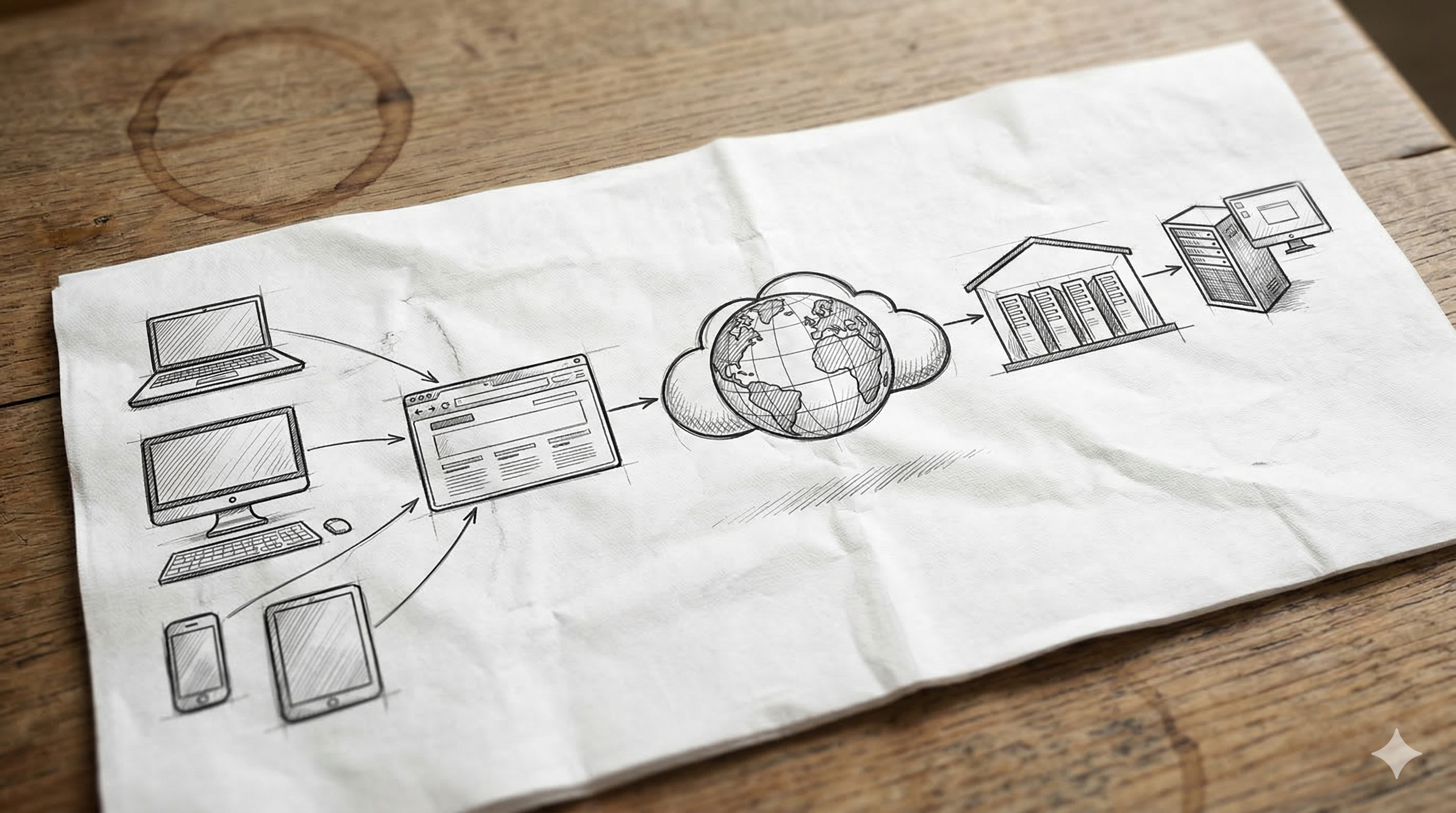
If you are an IT administrator tasked with securing your organization's fleet of devices, moving to a Zero Trust architecture is likely at the top of your list. Cloudflare’s WARP client is the essential cornerstone of that strategy, connecting devices securely to your Cloudflare One organization.
Rolling out the WARP client to five devices is trivial. Rolling it out to 5,000 is a challenge.
This is where Managed Deployments via Mobile Device Management (MDM) tools like Microsoft Intune, Jamf, or Kandji become essential. Instead of relying on end-users to download, install, and correctly configure the client (a process prone to error and support tickets), an MDM deployment allows you to push a pre-configured, standardized state to every device instantly. You ensure that every machine connects to the correct organization with the correct security posture from day one.
The Problem: The Building of the mdm.xml
For macOS and mobile devices, configuring managed settings is often done through standard .mobileconfig profiles or key-value pairs in the MDM interface. Windows, however, often requires a different approach.
On Windows, the Cloudflare WARP client looks for its instructions in a specific file located at C:\ProgramData\Cloudflare\mdm.xml.
This file dictates everything: which Zero Trust organization to join, whether the client should act as a full VPN or just encrypt DNS, and how the onboarding experience looks to the user.
The problem is that XML is notoriously brittle. A single missing bracket, a typo in a parameter name, or an incorrect value type can cause the configuration to fail silently. Administrators often find themselves manually copying examples from documentation sites, pasting them into Notepad++, and hoping they didn't make a syntax error. It’s a tedious, error-prone hurdle in an otherwise sleek deployment process.
The Solution: The Cloudflare MDM Configurator
The community has recognized this pain point. Instead of wrestling with raw XML, there is a better way: the Cloudflare MDM Configurator, hosted at https://mdm.dtg-lab.net/.
This community-developed tool transforms the complex task of writing XML into a simple, visual process. By using a straightforward web interface to select your desired settings, the tool automatically generates a perfectly formatted, syntax-error-free mdm.xml file ready for deployment.
It bridges the gap between abstract documentation parameters and the concrete file your Windows machines need.
Technical Deep Dive: Understanding the mdm.xml Parameters
Before we use the tool to automate the process, it is crucial to understand what we are actually configuring. The mdm.xml file tells the WARP system service how to behave before a user even logs in.
While there is a vast array of parameters available in the Cloudflare documentation, a few core settings define almost every deployment.
1. The Essentials: Organization Team Name
The most critical parameter is organization. Without this, the WARP client has no idea which Cloudflare account it belongs to.
<organization>your-team-name</organization>This is not your alphanumeric Account ID; it is the "Team name" you defined under Settings > Customization in the Zero Trust dashboard (e.g., if your access URL is https://acme-corp.cloudflareaccess.com, your team name is acme-corp).
2. Defining Behavior: Service Mode
How do you want WARP to act? The service_mode parameter dictates the traffic flow. It determines if WARP acts as a full tunnel, encrypting all traffic, or just secures DNS queries.
- Gateway with DoH (
1): The client encrypts DNS queries using DNS over HTTPS (DoH) and sends them to Cloudflare Gateway for DNS filtering. HTTP traffic does not go through the tunnel. - WARP (
2): The standard mode. All traffic is routed through the WARP WireGuard tunnel to Cloudflare Gateway. This is required for L7 firewall policies and traffic inspection. - Proxy Mode (
3): Used in specific legacy configurations where WARP acts as a local SOCKS5 proxy.
Getting this integer wrong in the XML means deploying a fundamentally incorrect security posture to your fleet.
3. User Experience: Onboarding and Auto-Connect
You can significantly reduce admin overhead by controlling what the user sees first.
onboarding(Boolean): Set this tofalseto hide the initial "What is WARP?" splash screens. In a corporate environment, users don't need the sales pitch; they need to connect.auto_connect(Integer): Usually set to1(minutes). This ensures that if the WARP client is turned off for any reason, it automatically re-engages after a short period, ensuring compliance.
Admin’s Guide: Generating Your File with the Configurator
Now that we understand the parameters, let's look at how the Cloudflare MDM Configurator simplifies putting them together. For full transparency, the code base for this tool is open-source and available for analysis on GitHub here: https://github.com/Dgilmore-CF/cf-mdm-configurator-html.
Here is a typical workflow for an admin preparing a Windows deployment for the fictitious "Acme Corp."
Step 1: Define the Core Identity Upon opening the tool, the first request is the most important: the Organization Team Name. We enter acme-corp.
Step 2: Select the Service Mode Visually Instead of remembering if "full WARP" is integer 1 or 2, the tool provides a clear dropdown menu. We select Gateway with WARP to ensure full traffic inspection. The tool handles the underlying integer mapping automatically.
Step 3: Toggle User Experience Settings We want a silent deployment. We scroll to the Onboarding section and simply toggle the switch to "Disabled." Next, we enable Auto Connect and set the value to 1 minute to ensure connectivity is maintained.
Step 4: Add Support Information To reduce helpdesk calls, we can leverage the support_url parameter. In the tool, we find the Support URL field and paste in our internal wiki link: https://wiki.acme-corp.com/vpn-help.
Step 5: Generate and Download Once the visual switches match our desired policy, we click the Generate MDM file button.
Instantly, the tool provides a preview of the XML. We can see that it has correctly formatted our inputs:
We click download to save the mdm.xml file.
<?xml version="1.0" encoding="UTF-8"?>
<dict>
<key>organization</key>
<string>acme-corp</string>
<key>service_mode</key>
<integer>2</integer>
<key>onboarding</key>
<false/>
<key>auto_connect</key>
<integer>1</integer>
<key>support_url</key>
<string>https://wiki.acme-corp.com/vpn-help</string>
</dict>Step 6: Deployment The final step is to take this pristine XML file and load it into your MDM of choice (like Intune). You will configure your MDM to copy this file into the C:\ProgramData\Cloudflare\ directory on target Windows machines after the WARP .msi installer has run.
Conclusion
Managed deployments are vital for Zero Trust adoption at scale. While Windows configuration via XML presents a unique hurdle, tools like the Cloudflare MDM Configurator remove the complexity and risk of manual editing. By understanding the core parameters and utilizing this community resource, administrators can ensure faster, more reliable, and more secure WARP rollouts.
Leave a Comment
Your comment will be reviewed before appearing on the site.

Comments
Be the first to comment on this post!